ShieldKit: The Open-Source Security Suite Your Toolchain Pretends to Be

A Quick Thank You
A genuine nod to the open-source community. ShieldKit exists because people at Anchore, Aqua Security, ProjectDiscovery, Bridgecrew, OWASP ZAP, DuckDB Labs, and the Prowler/ScoutSuite projects decided to build world-class security tools and just... give them away. Every scanner ShieldKit wraps, every library it imports — someone else built that. This project is standing on shoulders, and I'm not pretending otherwise.
You know what's fun? Dropping six figures on a "security platform" that runs three open-source scanners behind a login page and calls it "AI-powered." Even more fun when your team uses one of them, once a quarter, the week before audit.
The tools are already free. Syft, Grype, Trivy, Nuclei, Checkov, Prowler, ScoutSuite, ZAP — all open-source. What nobody builds is the glue. The part where results from eight scanners land in one database, reports generate themselves in three formats, and an AI analyst can actually query your findings instead of summarizing a PDF you won't read anyway.
That's ShieldKit. github.com/Parthasarathi7722/shieldkit
What It Does (One Paragraph, Because You'll Skim Anyway)
Eight security scanners (Syft, Grype, Trivy, Nuclei, Checkov, Prowler, ScoutSuite, OWASP ZAP), a cloud posture engine, a log analytics pipeline, an AI-powered SOC analyst, and a report generator — all in a single FastAPI server with a 10-tab browser UI. docker compose up, open localhost:8000, start scanning. Ships in mock mode by default so you can demo it in 30 seconds without installing a single tool.
The Dashboard tab — severity cards, scan history, activity feed. All live data from DuckDB.
The Scanners
SBOM generation (Syft), dependency analysis (Grype), container scanning (Trivy), URL/network scanning (Nuclei), IaC checks (Checkov), cloud posture audits (Prowler + ScoutSuite across AWS/Azure/GCP), and DAST via OWASP ZAP with three scan profiles, two execution modes, and five auth methods. Every scanner is an async Python class. Results normalize into a common schema and flow into DuckDB.
Nothing here is new. What's new is they all talk to the same database.
How a Scan Actually Works
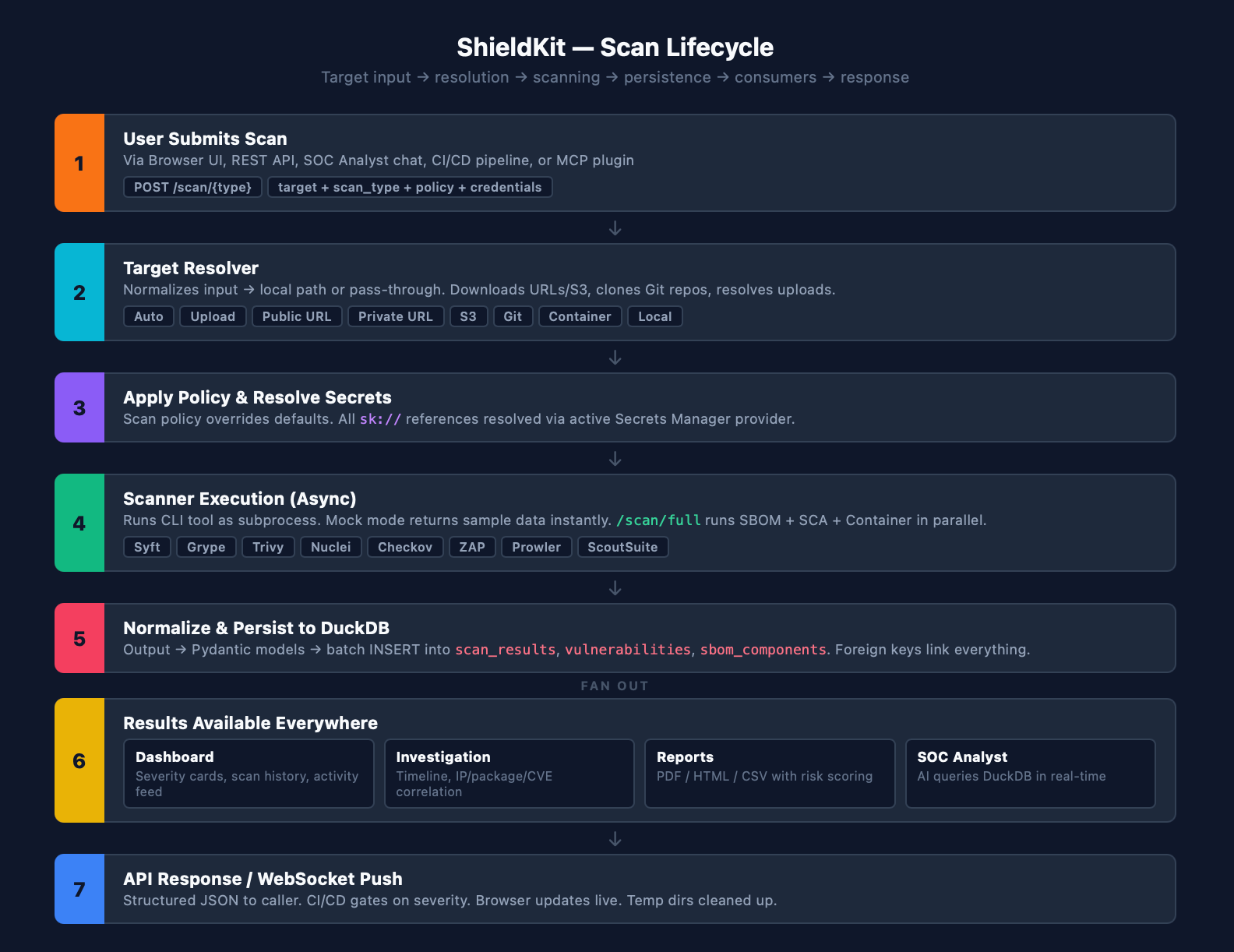
From target input to DuckDB persistence — 7 steps, fully async.
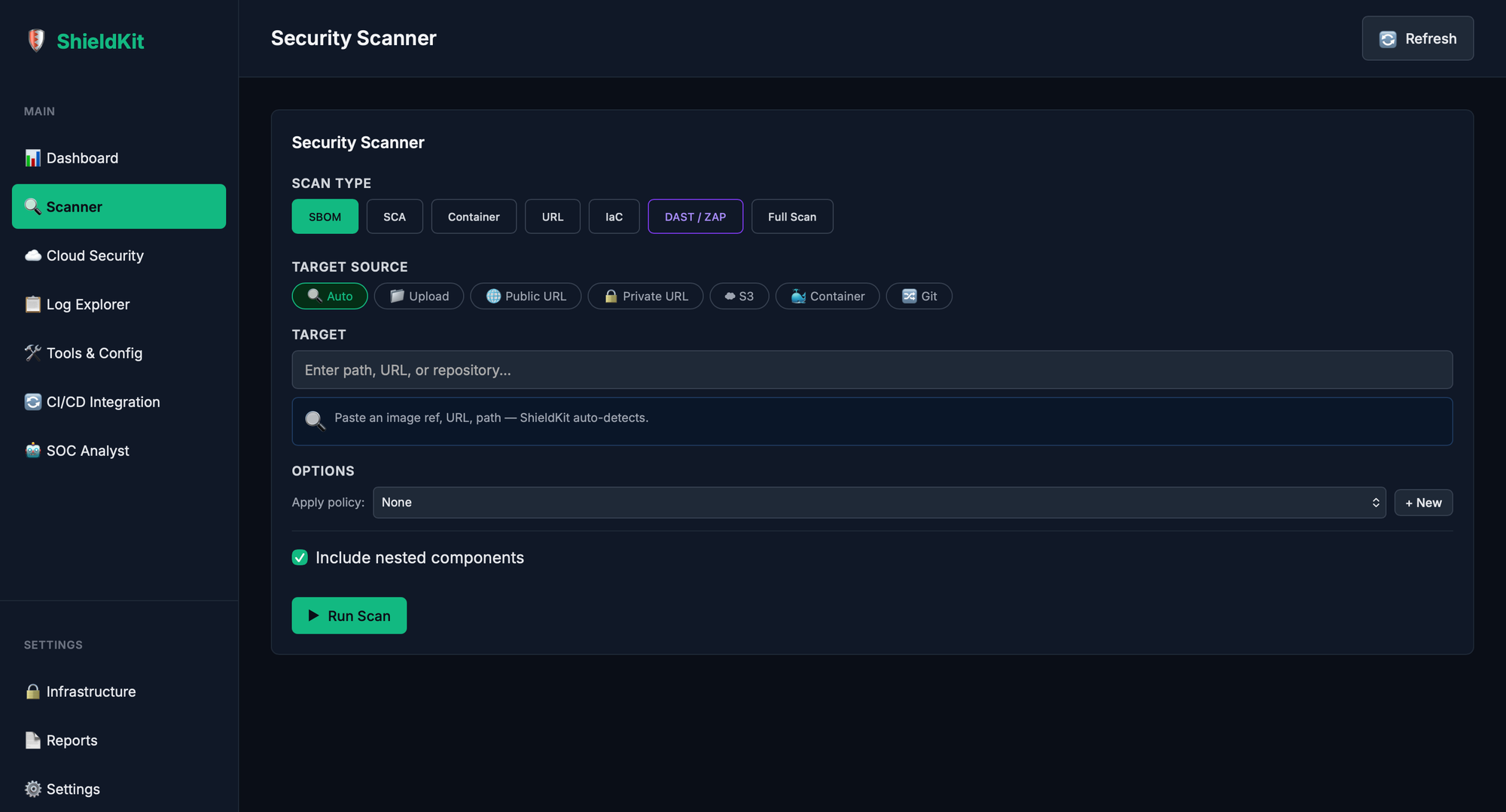
Scan Any Target From Anywhere
Most tools accept exactly one input type — a Docker image name or a local path. Helpful. ShieldKit's Target Resolver accepts eight: auto-detect, file upload, public URL, private URL with auth, S3 URI, Git repo (with token injection for private repos), container image, and local path.
Upload a tarball from the browser. Point it at an S3 bucket. Clone a private GitHub repo mid-scan. The resolver downloads, extracts archives for IaC scans, cleans up temp directories, and hands the scanner a local path. You just type a target and pick a pill.
The Scanner tab auto-filters target type options based on what scan you're running. Typing an s3:// URI in auto mode? It suggests switching to S3. Pasting a GitHub URL? It nudges you toward Git clone. It also shows contextual hints — accepted formats, example values, even the docker save command you'll need for container file uploads.
Credential Profiles make private targets reusable. Store a GitHub token or AWS keys as a named profile in the Secrets Manager, reference it by name in any scan request. No more re-entering credentials every time you scan a private repo.
DuckDB, Not Elasticsearch
ShieldKit uses DuckDB — embedded, zero-config, runs in-process, handles analytical queries on millions of rows without needing a cluster. Every scan result, vulnerability, SBOM component, cloud finding, and log entry sits in the same database with proper foreign keys.
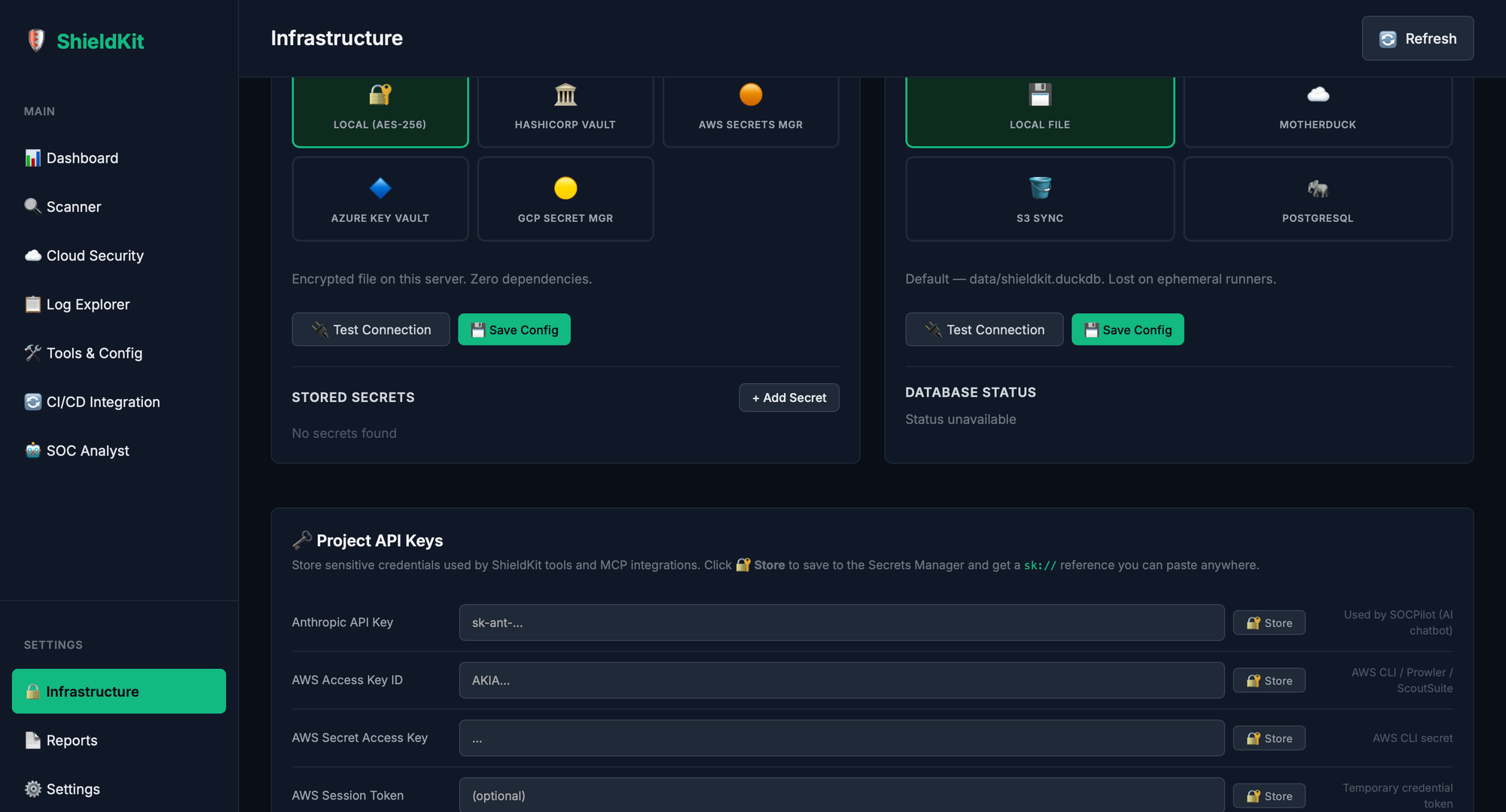
Four persistence backends if local DuckDB isn't enough: MotherDuck (cloud DuckDB), S3 Sync (download on startup, upload on shutdown), and PostgreSQL (DuckDB ATTACH for hybrid queries). Switch from the Infrastructure tab. No migration scripts.
Report Generator (Because Auditors Don't Read Dashboards)
Five report types: Vulnerability, SBOM Inventory, Cloud Findings, Executive Summary, and Full (everything). Three output formats: CSV, HTML, and PDF. Filter by date range, severity, target, scan type, or specific scan IDs.
The Executive Summary auto-computes a risk score from your critical/high ratio, surfaces the top 10 CVEs by CVSS, and breaks down scan activity by type. The HTML reports ship with print-optimized CSS. The PDFs have a proper cover page, severity-colored KPI cards, and paginated tables.
Generate from the Reports tab or hit POST /reports/generate. Reports persist to data/reports/ with a management API — list, download, delete. Your auditor gets a PDF. Your CISO gets the executive summary. Your dev team gets the CSV they'll import into a spreadsheet and argue about.
Secrets Manager (Your .env Is in Git, I Checked)
Five provider backends: Local AES-256 encryption, HashiCorp Vault (KV v2, pure REST, no SDK), AWS Secrets Manager, Azure Key Vault, GCP Secret Manager.
The trick: sk:// references. Store a secret, reference it as sk://my_api_key in any tool config. At scan time, ShieldKit resolves it through whatever provider you've configured. Switch from local to Vault? Tool configs don't change.
SOC Analyst (An AI That Actually Runs Your Tools)
Not another chatbot glued to a knowledge base. ShieldKit's SOC Analyst is an agentic loop (up to 8 iterations) powered by Anthropic's API with direct access to ShieldKit's scanning tools. Ask it to scan an image — it actually runs Grype. Ask what's critical in your last scan — it queries DuckDB. Ask it to investigate a CVE — it correlates across scans, logs, and packages.
Streams over WebSocket. Calls tools. Reasons over results. Doesn't hallucinate scan data because it's reading from your database.
CI/CD Config Generator
Pick a platform, check your scan types, click Generate. Eight platforms: GitHub Actions, Jenkins, GitLab CI, Bitbucket Pipelines, ArgoCD, CircleCI, Azure DevOps, AWS CodeBuild. Each produces valid YAML/Groovy/JSON with health checks, environment variables, and API calls pre-configured. Security scanning in 3 lines of your pipeline instead of 30 lines of YAML from a Medium article.
Log Analytics Without the ELK Tax
Ingests from S3/CloudTrail, Syslog, JSONL files, and webhooks. Auto-detects format, parses, normalizes, batch-inserts into DuckDB. Investigation endpoints for timelines, IP correlation, package tracing, and CVE blast radius analysis. No Elasticsearch. No Logstash. No Kibana eating 4GB of RAM to render a pie chart.
Scan Policies
Named, reusable scan configurations per tool. Create "production-strict" with critical-only severity filters, create "dev-permissive" with everything enabled. Policies can even store a default target — apply the policy and the target field pre-fills automatically. No more "which flags did we use for the audit?"
The UI: 10 Tabs, One HTML File
Single-file SPA. No React. No webpack. No node_modules. Ten tabs: Dashboard, Scanner, Cloud Security, Log Explorer, Tools & Config, CI/CD Integration, SOC Analyst, Infrastructure, Reports, Settings. Everything over HTTP and WebSocket to the FastAPI backend.
MCP Plugin
ShieldKit exposes all its tools as an MCP (Model Context Protocol) plugin. Any MCP-compatible agent — like SOCPilot — can call shieldkit_sca or shieldkit_cloud_scan and get structured JSON back. python -m mcp_plugin and your AI agent has a security toolkit.
The Architecture (Big Picture)
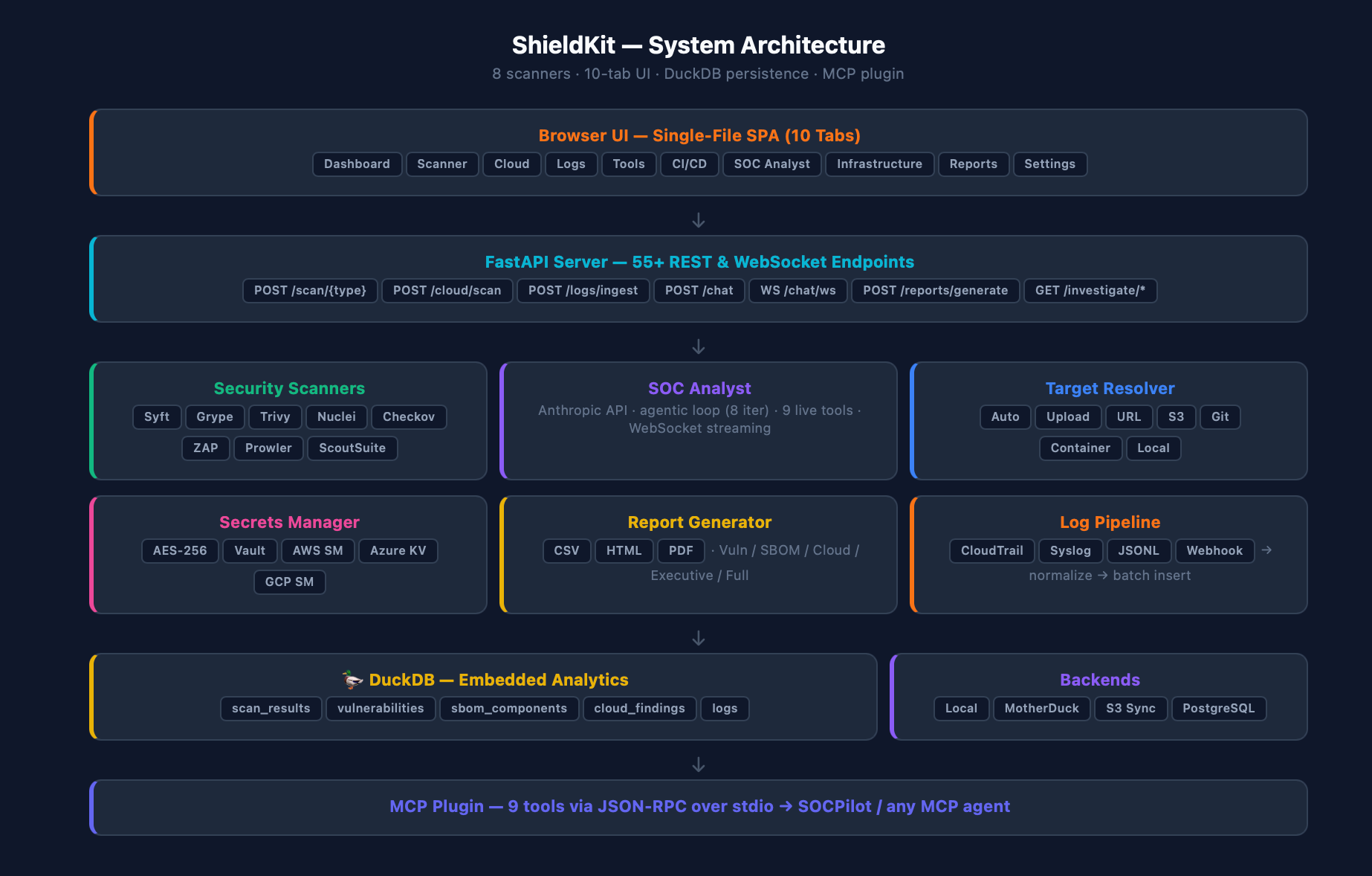
Browser UI → FastAPI (55+ endpoints) → 8 scanners + services → DuckDB + MCP plugin.
Getting Started
git clone https://github.com/Parthasarathi7722/shieldkit.git
cd shieldkit
docker compose up
# localhost:8000 — you're in
Want DAST? docker compose --profile tools up. Want local dev? pip install -r requirements.txt && python run.py. Set SHIELDKIT_MODE=live when you're done pretending with mock data.
The repo includes ARCHITECTURE.md with 9 Mermaid diagrams if you're the kind of person who reads those (respect).
Why Bother
The security tool market is broken in a very specific way: the individual tools are excellent and free, but the moment you want them to talk to each other — shared database, unified UI, CI/CD automation, AI investigation, actual reports — you're suddenly looking at enterprise contracts with "contact sales" pricing.
ShieldKit is the glue. It doesn't replace Grype or Prowler. It gives them a shared brain, a shared interface, and an AI analyst that can work across all of them. Now it also gives them a report generator that produces PDFs your auditors can actually read, and a target resolver that can pull from S3, Git, or a file upload without you writing a download script.
Will it replace Splunk? No. Will it give a 3-person security team 80% of what they need without a procurement cycle? Absolutely.
Star it, break it, open issues: github.com/Parthasarathi7722/shieldkit
Partha Sarathi Das writes about DevSecOps, cloud security, and building tools that don't require a budget committee. More at chaostocontrol.ghost.io.